Linux Firewalls: What You Need to Know About Iptables and Firewalld
Introduction
All modernistic operating systems come equipped with a firewall – a software application that regulates network traffic to a computer. Firewalls create a barrier between a trusted network (like an function network) and an untrusted one (like the internet). Firewalls piece of work by defining rules that govern which traffic is allowed, and which is blocked. The utility firewall developed for Linux systems is iptables.
In this tutorial, learn how how to install iptables, configure, and utilize iptables in Linux.
Prerequisites
- A user business relationship with sudo privileges
- Admission to a final window/command line (Ctrl-Alt-T, Ctrl-Alt-F2)
How iptables Work
Network traffic is fabricated up of packets. Data is broken up into smaller pieces (chosen packets), sent over a network, then put back together. Iptables identifies the packets received and and so uses a prepare of rules to determine what to do with them.
Iptables filters packets based on:
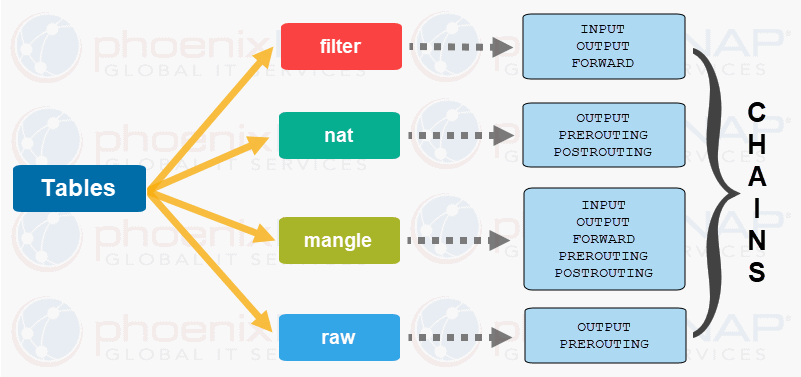
- Tables: Tables are files that bring together similar actions. A table consists of several chains.
- Chains: A concatenation is a cord of rules. When a package is received, iptables finds the appropriate table, and so runs it through the chain of rules until information technology finds a match.
- Rules: A rule is a statement that tells the system what to do with a packet. Rules can block one type of parcel, or forward some other type of packet. The upshot, where a packet is sent, is called a target.
- Targets: A target is a decision of what to do with a packet. Typically, this is to take it, drib it, or reject it (which sends an mistake back to the sender).
Tables and Chains
Linux firewall iptables has four default tables. We will listing all four along with the chains each table contains.
one. Filter
The Filter table is the most frequently used one. It acts as a bouncer, deciding who gets in and out of your network. It has the following default chains:
- Input – the rules in this chain control the packets received by the server.
- Output – this chain controls the packets for outbound traffic.
- Forward – this fix of rules controls the packets that are routed through the server.
two. Network Address Translation (NAT)
This table contains NAT (Network Address Translation) rules for routing packets to networks that cannot be accessed directly. When the destination or source of the packet has to be altered, the NAT table is used. Information technology includes the following bondage:
- Prerouting – this chain assigns packets equally soon every bit the server receives them.
- Output – works the same as the output chain we described in the filter tabular array.
- Postrouting – the rules in this chain allow making changes to packets after they leave the output chain.
3. Mangle
The Mangle table adjusts the IP header properties of packets. The table has all the following chains nosotros described above:
- Prerouting
- Postrouting
- Output
- Input
- Forward
iv. Raw
The Raw table is used to exempt packets from connectedness tracking. The raw tabular array has two of the bondage we previously mentioned:
- Prerouting
- Output
5. Security (Optional)
Some versions of Linux also utilize a Security tabular array to manage special access rules. This table includes input, output, and frontwards chains, much like the filter table.
Targets
A target is what happens after a bundle matches a rule criteria. Non-terminating targets keep matching the packets against rules in a chain even when the packet matches a rule.
With terminating targets, a bundle is evaluated immediately and is not matched against some other chain. The terminating targets in Linux iptables are:
- Accept – this rule accepts the packets to come up through the iptables firewall.
- Drop – the dropped package is not matched against whatever further chain. When Linux iptables drop an incoming connexion to your server, the person trying to connect does not receive an mistake. It appears as if they are trying to connect to a non-existing motorcar.
- Return – this dominion sends the packet dorsum to the originating chain so you tin match it against other rules.
- Refuse – the iptables firewall rejects a bundle and sends an error to the connecting device.
How to Install and Configure Linux Firewall iptables
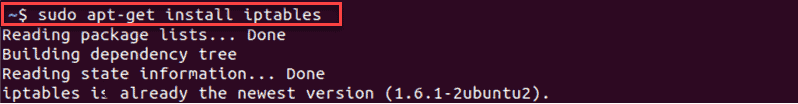
Installing Iptables Ubuntu
Iptables are installed default on virtually Linux systems. To confirm that iptables is installed, apply the post-obit command:
sudo apt-get install iptables The example output in Ubuntu confirms that the latest version of iptables is already present:
If you want to keep iptables firewall rules when you reboot the system, install the persistent packet:
sudo apt-get install iptables-persistent Installing Iptables CentOS
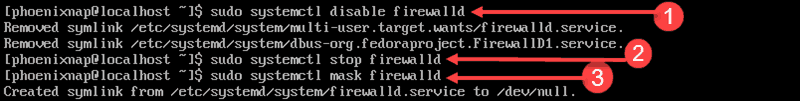
In CentOS vii, iptables was replaced past firewalld.
To install iptables, first you demand to stop firewalld. Enter the following commands:
sudo systemctl finish firewalld sudo systemctl disable firewalld sudo systemctl mask firewalld The commands stop and prevent firewalld from starting at boot, and do not permit other services get-go firewalld.
Adjacent, install and enable iptables. First, install the iptables services package with the following command:
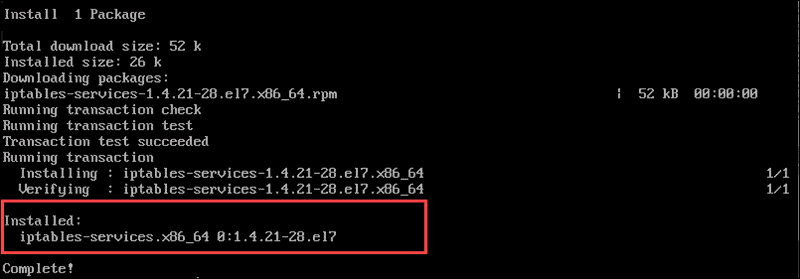
sudo yum -y install iptables-services This bundle preserves your rules after a system reboot. The information displayed beneath confirms that the installation is complete:
Enter the following commands to enable and start iptables in CentOS 7:
sudo systemctl enable iptables sudo systemctl start iptables The status command confirms the status of the application:
sudo systemctl status iptables 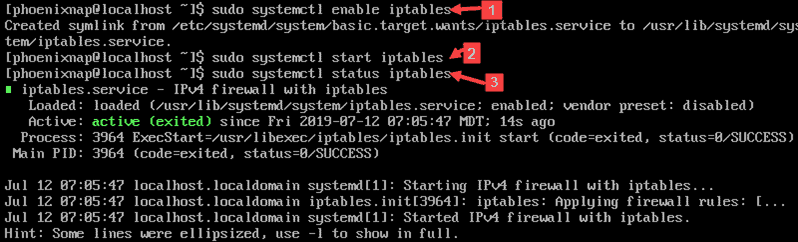
Notation:There are two unlike versions of iptables, for IPv4 and IPv6. The rules we are roofing in this Linux iptables tutorial is for IPv4.
To configure iptables for IPv6, you need to apply the iptables6 utility. These two dissimilar protocols practice not piece of work together and accept to be configured independently.
Basic Syntax for iptables Commands and Options
In general, an iptables control looks as follows:
sudo iptables [choice] CHAIN_rule [-j target] Hither is a list of some common iptables options:
-
-A --append– Add a rule to a chain (at the terminate). -
-C --check– Look for a rule that matches the concatenation'due south requirements. -
-D --delete– Remove specified rules from a chain. -
-F --affluent– Remove all rules. -
-I --insert– Add together a rule to a chain at a given position. -
-L --list– Show all rules in a chain. -
-Due north -new-chain– Create a new chain. -
-v --verbose– Bear witness more information when using a list pick. -
-X --delete-concatenation– Delete the provided concatenation.
Iptables is case-sensitive, so make sure you lot're using the correct options.
Configure iptables in Linux
By default, these commands touch on the filters table. If you need to specify a different table, use the –t selection, followed by the name of the tabular array.
Check Electric current iptables Status
To view the electric current set of rules on your server, enter the following in the terminal window:
sudo iptables -L 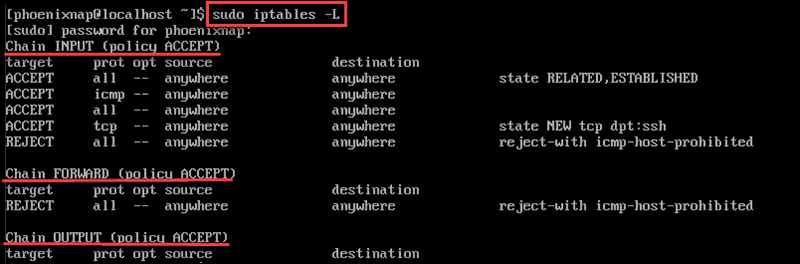
The arrangement displays the status of your chains. The output volition list three chains:
Concatenation INPUT (policy Take) Chain FORWARD (policy Have) Chain OUTPUT (policy ACCEPT) Enable Loopback Traffic
It's safe to allow traffic from your own organization (the localhost). Append the Input concatenation by entering the following:
sudo iptables -A INPUT -i lo -j Have This command configures the firewall to accept traffic for the localhost ( lo ) interface ( -i ). Now anything originating from your arrangement will pass through your firewall. You need to set this rule to allow applications to talk to the localhost interface.
Allow Traffic on Specific Ports
These rules allow traffic on different ports you specify using the commands listed below. A port is a communication endpoint specified for a specific type of data.
To allow HTTP spider web traffic, enter the following command:
sudo iptables -A INPUT -p tcp --dport 80 -j ACCEPT To allow only incoming SSH (Secure Beat out) traffic, enter the post-obit:
sudo iptables -A INPUT -p tcp --dport 22 -j Take To permit HTTPS net traffic, enter the following command:
sudo iptables -A INPUT -p tcp --dport 443 -j Have The options piece of work as follows:
-
-p– Cheque for the specified protocol (tcp). -
--dport– Specify the destination port. -
-j jump– Have the specified action.
Control Traffic by IP Address
Use the following command to ACCEPT traffic from a specific IP address.
sudo iptables -A INPUT -s 192.168.0.27 -j ACCEPT Replace the IP accost in the command with the IP address you desire to allow.
You lot can too Drib traffic from an IP address:
sudo iptables -A INPUT -s 192.168.0.27 -j DROP You can Pass up traffic from a range of IP addresses, but the command is more than complex:
sudo iptables -A INPUT -thou iprange --src-range 192.168.0.1-192.168.0.255 -j Reject The iptables options nosotros used in the examples piece of work as follows:
-
-g– Lucifer the specified option. -
-iprange– Tell the system to wait a range of IP addresses instead of a unmarried i. -
--src-range– Identifies the range of IP addresses.
Dropping Unwanted Traffic
If y'all define dport iptables firewall rules, you need to prevent unauthorized access by dropping any traffic that comes via other ports:
sudo iptables -A INPUT -j DROP The -A option appends a new rule to the chain. If whatsoever connection comes through ports other than those y'all defined, it volition exist dropped.
Delete a Rule
You can use the -F choice to clear all iptables firewall rules. A more precise method is to delete the line number of a rule.
First, list all rules by entering the following:
sudo iptables -Fifty --line-numbers 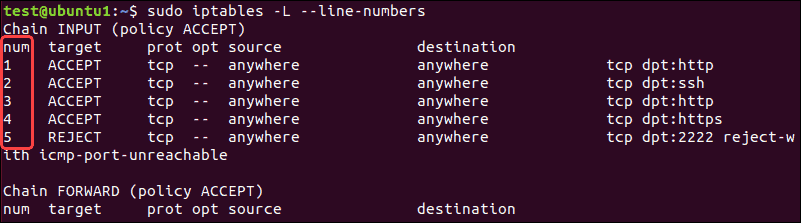
Locate the line of the firewall rule y'all want to delete and run this command:
sudo iptables -D INPUT <Number> Replace <Number> with the actual rule line number you desire to remove.
Save Your Changes
Iptables does not keep the rules you created when the organization reboots. Whenever you lot configure iptables in Linux, all the changes you make apply but until the commencement restart.
To save the rules in Debian-based systems, enter:
sudo /sbin/iptables–save To save the rules in Carmine-Lid based systems, enter:
sudo /sbin/service iptables save The side by side time your organization starts, iptables will automatically reload the firewall rules.
Conclusion
Afterward reading this Linux iptables tutorial, yous should have a meliorate understanding of how iptables work and how to install the iptables tool.
Y'all can now also configure bones iptables firewall rules for your Linux system. Feel free to experiment, as yous can always delete rules that you lot do not need, or flush all rules and start over again.
Was this article helpful?
Yes No
Source: https://phoenixnap.com/kb/iptables-tutorial-linux-firewall
0 Response to "Linux Firewalls: What You Need to Know About Iptables and Firewalld"
Postar um comentário